
Flatfile
Robert Trencheny
"We're using inlets Pro to power our staging environments and give people preview build URLs. It's going great!"
Self-hosted HTTP and TCP tunnels with full control and privacy. Expose endpoints publicly, or tunnel customer services back to your SaaS.
Trusted by teams at






From webhooks and local Kubernetes to hybrid cloud and private customer connectivity.
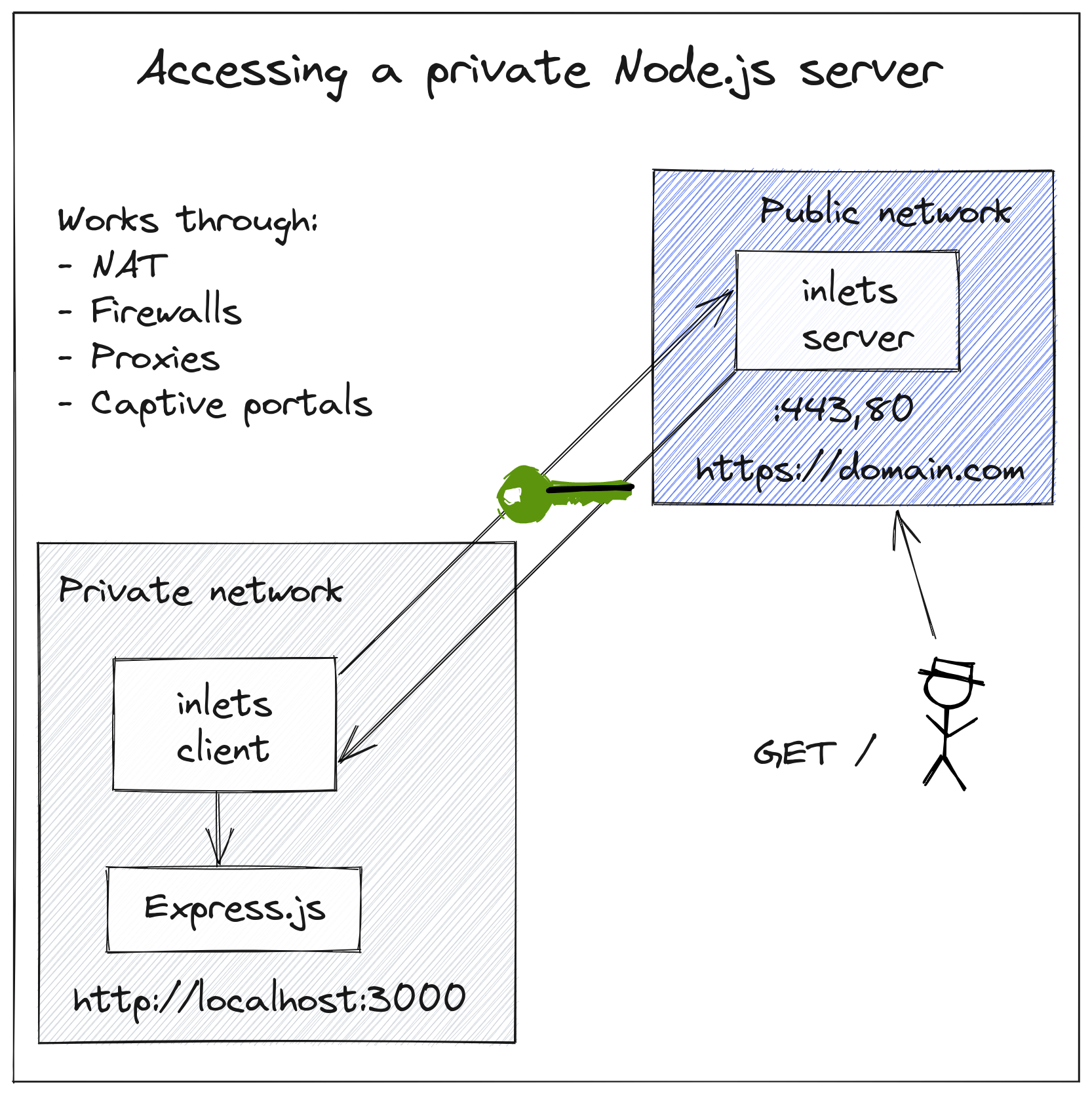
inlets exposes HTTP and TCP services without dragging whole subnets, hosts or teams into a VPN.
Your tunnels are secured by default so anything that you transfer over them is encrypted. And they'll work through the toughest network conditions such as NAT, firewalls and corporate proxies.
It was built for the cloud, which means it works well on bare-metal, in a container, on Kubernetes and has built-in support for Prometheus metrics, so you can monitor and measure your tunnels.
Connect hundreds or thousands of private customer networks or devices to your SaaS, via internal services in your cluster.
Connect private clusters and deploy applications from a central control plane without opening inbound access.
Not only can you share websites, blog posts drafts and APIs without publishing them on public cloud, but you can integrate directly with webhooks from Stripe, GitHub and Slack.
Make the most of your existing hardware investment, by bringing real traffic to your local machines.
Connect legacy applications, GPUs or private test environments to your public cloud account.
Get a cloud LoadBalancer for your local self-hosted Kubernetes cluster.
Use inlets Pro for your own services and environments. Use Uplink when your product needs to connect to customer networks.
| Category | inlets Pro | Uplink |
|---|---|---|
| Best for | Webhooks, previews, homelabs | Connect to customers, hybrid cloud, service providers |
| Server | Tunnel server hosted in a public cloud VM | Your own Kubernetes cluster |
| Client | Windows, macOS, Linux, containers, Kubernetes | Windows, macOS, Linux, containers, Kubernetes |
| Scale | Small numbers of tunnels | 10+ tunnels, scales to thousands |
| Endpoints | Public or private | Private by default |
| Multi-tenant | No | Yes |
| Management | Manual / self-service | Managed control plane |
| Provisioning | CLI | Tunnel CLI, REST API, Kubernetes Custom Resource |
| Starting price | 125 USD / mo, includes 5 tunnels | 250 USD / mo, includes 10 tunnels |
Read the inlets Pro docs or the Uplink docs.
Developers use inlets for previews, webhooks and local clusters. SaaS teams use it to reach private customer environments without another VPN project.

Flatfile
Robert Trencheny
"We're using inlets Pro to power our staging environments and give people preview build URLs. It's going great!"

Riskfuel
Addison van den Hoeven
"Riskfuel is using inlets to train machine learning models with millions of data points for clients over secure tunnels."
Cloodot
Haris
"We use inlets instead of Ngrok while developing with webhooks for our live chat product."

VSHN
Tobias Brunner
"Our customers' VPCs do not allow any incoming connections, so we use inlets to connect their OpenShift clusters to our product."

Banzai Cloud
Janos Matyas
"We can test our code locally without rebuilding and redeploying it for every change."

Sixgill
Jordan Gregory
"inlets Pro makes it easy for us to provide secure service and support of our Sense AI Platform deployed through cloud marketplaces."
A few practical examples covering customer connectivity, securing exposed services, and private Kubernetes access.
Quickstart: automate and scale tunnels with Inlets Uplink
A practical guide for the multi-tenant Uplink model: namespaces, APIs, private services and controlled customer connectivity.
Secure HTTP tunnels with OAuth
Protect demos, preview environments and internal tools with GitHub OAuth, basic auth, bearer tokens and IP allow lists.
Expose ArgoCD on the Internet with Inlets and Istio
A concrete walkthrough for exposing private cluster services safely with Kubernetes-native tooling and real ingress patterns.
Explore common setups for Uplink, HTTPS, TCP and Kubernetes.
Create a tenant-scoped tunnel, hand the customer a command, then consume the service privately from inside your cluster.
# tunnel resource
apiVersion: uplink.inlets.dev/v1alpha1
kind: Tunnel
metadata:
name: acmeco
namespace: tunnels
spec:
tcpPorts:
- 8080
# customer connects to the router
inlets-pro uplink client \
--url wss://uplink.example.com/tunnels/acmeco \
--upstream http://127.0.0.1:8080 \
--token-file ./token.txt
# private access from inside the cluster
kubectl run -t -i curl --rm \
--image ghcr.io/openfaas/curl:latest /bin/sh
curl -i http://acmeco.tunnels:8000Short answers for the two most common paths: self-hosted tunnels with Pro, or multi-tenant customer connectivity with Uplink.
Get Started
Self-hosted tunnels for development and infrastructure. A Kubernetes-native control plane for private customer connectivity.